-
5G & Massive IoT Business

Is 5G security being sacrificed at the altar of profit, politics and process?
Homo sapiens is an incredibly adaptable species, arguably the most adaptable ever. But it is also a forgetful one, quick to take things for granted. Many of us can remember when cell phones first emerged, when the internet first became publicly available, when the first iPhone was released. These momentous shifts occurred within a generation, altering the nature of society and civilization. Just a few decades ago, none of these existed, but by the time…
Read More » -
5G Security

Can we afford to keep ignoring Open RAN security?
I’m skeptical of ‘futurists’. Work closely enough with the development of technology solutions and you’ll know that the only certain thing about the future is that it’s constantly changing. For example, few ‘futurists’ predicted the Covid-19 outbreak that brought the world to a standstill in 2020. Many, however, had spent hours waxing on about how 5G technology was to change the trajectory of human evolution, telling tales of what would be possible with ultra-high speed,…
Read More » -
Society 5.0

Securing Society 5.0 – Overcoming the hidden threats in society’s greatest evolutionary leap
A term first coined by the Japanese government, “Society 5.0” describes “A human-centered society that balances economic advancement with the resolution of social problems by a system that highly integrates cyberspace and physical space.” The fifth evolution of the society, enabled by the fifth generation of cellular networking and cyber-physical systems, imagines technology, things and humans converging to address some of the biggest societal challenges. The concept encompasses Industry 4.0, Fourth Industrial Revolution, Smart-Everything World…
Read More » -
5G & Massive IoT Business
Open RAN May Be the Future of 5G, but Can We Keep It Secure?
It’s been a year of contradictions for the telecommunications industry. Like most sectors, it has been heavily impacted by the consequences of the Covid-19 pandemic, with a slowdown in global 5G roll-outs being a notable result. Geopolitical conflicts have continued to muddy the market, with governments playing a more active role than ever in setting telecoms-centred policy. At the same time, however, the air is thick with promise and opportunity. Over the last nine months,…
Read More » -
Cyber-Kinetic Security
Cybersecurity and Safety in the 5G-Enabled Smart-Everything World
Neil Harbisson calls himself a cyborg. Without the antenna implanted in his skull, he would not be able to see colour of any kind. Born with achromatopsia, a condition of total colourblindness that affects 1 in every 30 000 people, Harbisson’s physical faculties are augmented by cyber technology to grant him access to a life of greater meaning and satisfaction. As technological evolution leads to concomitant advances in medical science, we are seeing more and…
Read More » -
5G Security
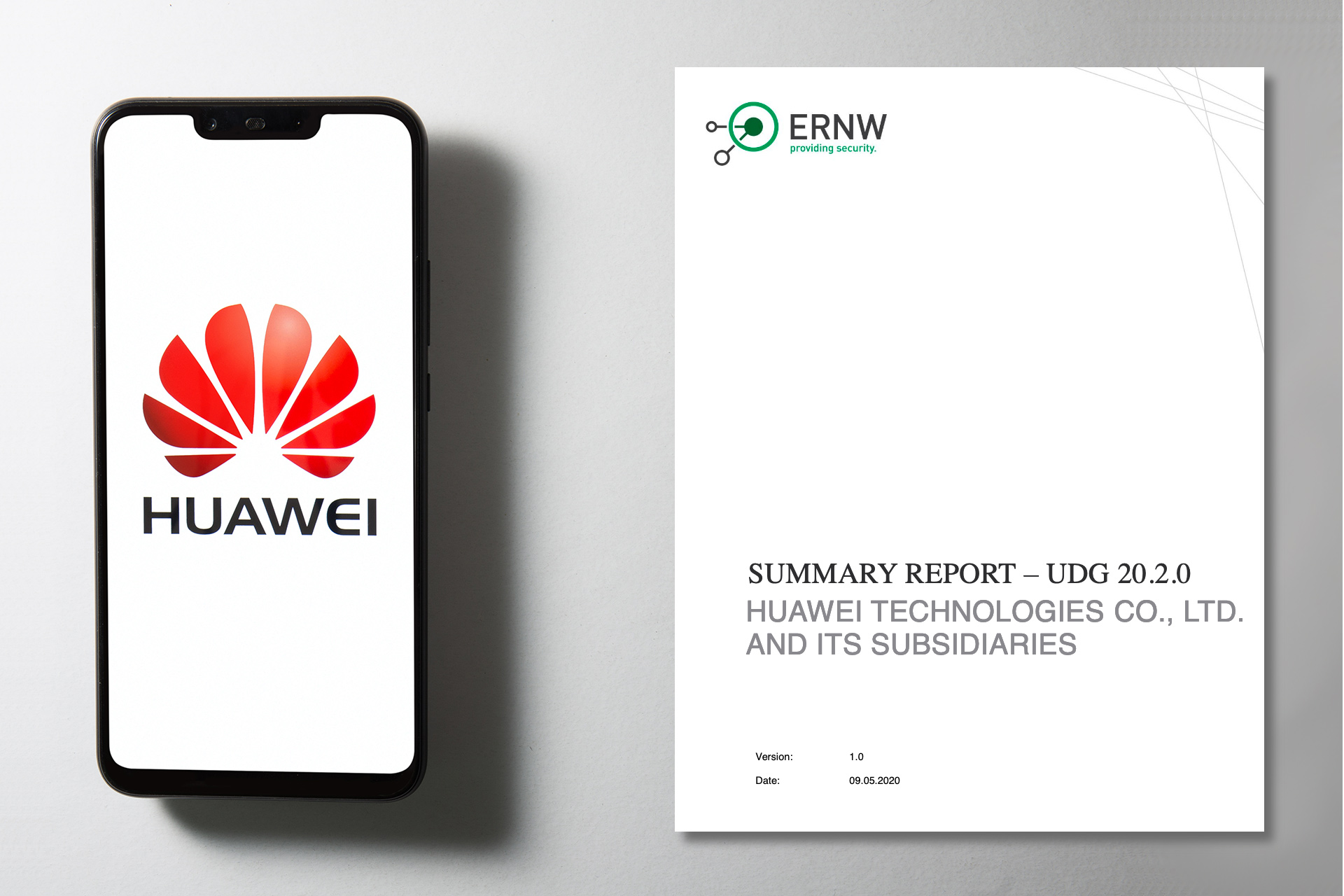
Does the positive review of Huawei UDG source code quality mean that Huawei 5G is secure and reliable?
No, no it doesn’t. Huawei’s code might as well be extremely secure. Their code is certainly the most scrutinized. But the recent UDG source code review is not an evidence of security. ERNW, an independent IT security service provider in Germany, recently performed a technical review / audit of Huawei’s Unified Distributed Gateway (UDG) source code. Huawei made the summary report available here [PDF]. The review focused on the quality of the source code and…
Read More » -
Society 5.0

Opportunity and Cybersecurity in the Age of 5G
The human will to innovate is seemingly relentless. The history of our species is one of continual development, with the last 350 years, in particular, representing staggering technological progress. The first industrial revolution mechanized production using natural elements like water. The second revolution used electricity to enable mass production; the third used electronics and information technology to automate production. The fourth industrial revolution unfolding all around us is characterized by an exponential growth in data…
Read More » -
Cyber-Kinetic Security
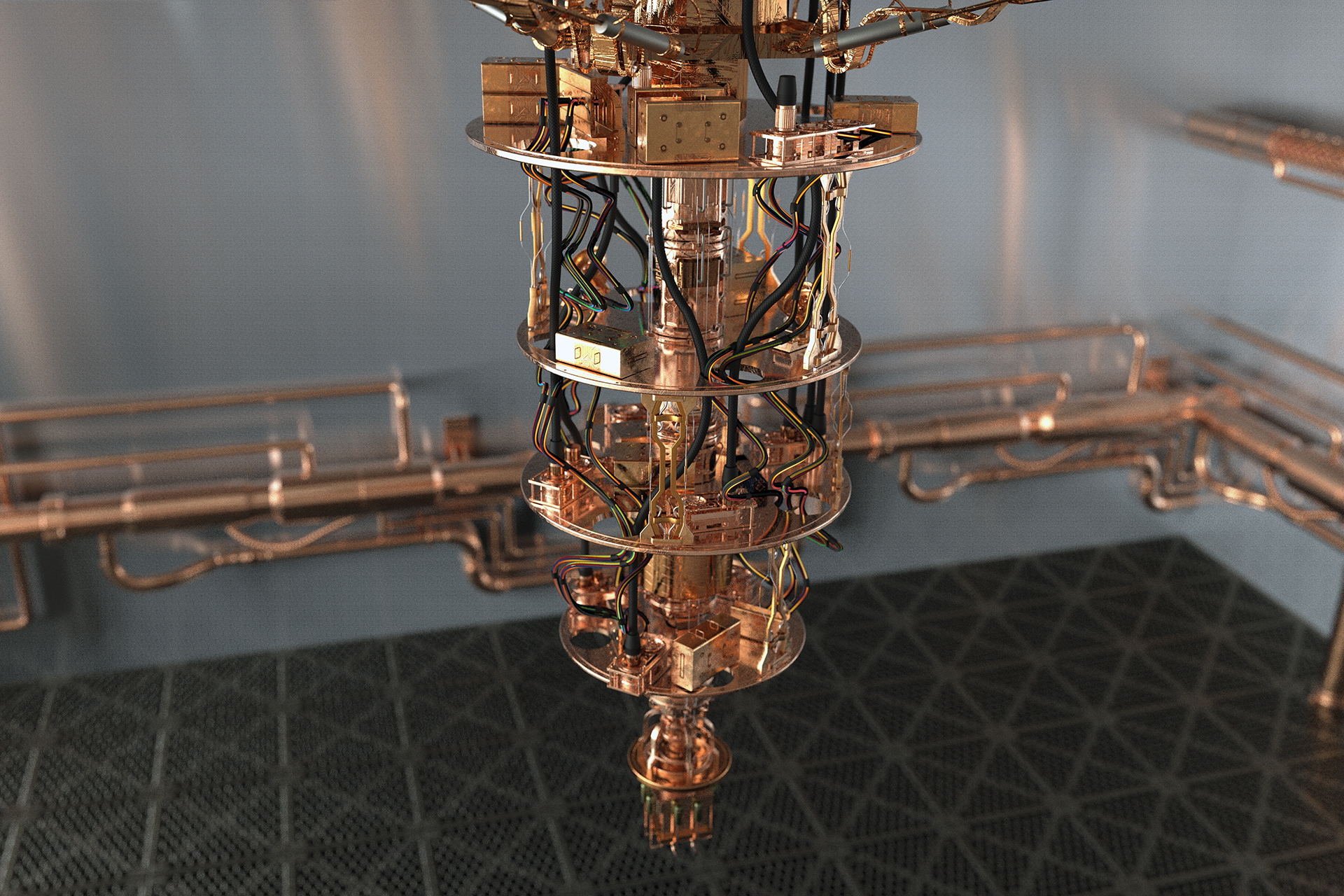
The Quantum Computing Threat
Recently, in the science journal Nature, Google claimed ‘quantum supremacy’ saying that its quantum computer is the first to perform a calculation that would be practically impossible for a classical machine. This quantum computing breakthrough brings us closer to the arrival of functional quantum systems which will have a profound effect on today’s security infrastructure. How will quantum computing affect the security of 5G technologies currently being developed and deployed? Last spring we suggested that…
Read More » -
Cyber-Kinetic Security

IIoT and Trust and Convenience: A Potentially Deadly Combination
When microwave ovens first arrived on the market in 1967 they were met with public skepticism. Perhaps it was because, not long before, the same technology now promising to safely cook consumers’ evening meals was the backbone of a military radar. Perhaps it was the $495 price tag (more than $3,700 in today’s money). Whatever the reason, in the early 1970s the percentage of Americans owning a microwave was tiny. By 2011, it was 97%.…
Read More » -
Cyber-Kinetic Security

5G Network: A Quantum Leap in Connectivity – and Cyber Threats
The timeline of human history is marked by inflection points of major technological advancement. The plow, the printing press, the telegraph, the steam engine, electricity, the telephone, the internet: each of these breakthroughs precipitated tectonic shifts in how people lived and worked. Now, in the early part of the 21st century, we stand witness to the birth of a new industrial revolution built on 5th generation cellular technology – 5G network. As the name implies,…
Read More »