Smart Home / Smart Building Connectivity Options and Their Cybersecurity

In a recent session on smart building cybersecurity, a student cheekily asked me “How did we ever connect anything before 5G?” At that moment I realized I might have been overdoing my 5G cheerleading recently. To atone, here are the key performance and cybersecurity attributes of the most commonly used connectivity technologies in smart home / smart building use cases… And 5G.
If you thought that the “traditional” home life is under heavy attack from digitization of media and constant communication, wait until you learn about the Internet of Things (IoT) and Smart Homes.
Our most personal spaces – our homes – are rapidly getting digitized and connected. Hundreds of IoT devices – sensors, actuators, smart speakers, smart toothbrushes, and smart everything are being implemented in every home. All trying to create an environment that caters to our every whim, predicts our needs, personalizes our physical space, monitors our health, conserves energy, etc. In doing so all constantly communicating with each other, with our mobile phones, and with a myriad of solutions located somewhere in “clouds”. All creating new cybersecurity and privacy risks.
Indeed, the most representative indicator of technology impact on daily life is the development of wireless communications as the enabler for all these transformations. After the emergence of radio and TV, it was the appearance of the 1st generation of cellular communications technology in 1980s that introduced analog mobile voice communication service and accelerated the transformation. In the next decade 2G offered digital communications and paved the way to the 3G—cellular technology from the beginning of the 21st century that provided IP support and wireless broadcast transmissions. Today the most widespread cellular technology is 4G (as the first all IP cellular technology) and the world is briskly preparing for deployment of its successor—5G.
Simultaneously with the development of cellular technologies, other wireless technologies shaped the market and enabled simple, ubiquitous, device-to-device communication at short ranges. In this article we’ll explore wireless connectivity options for smart homes / smart buildings and introduce main cybersecurity attributes of each.
Wireless technologies and smart home – smart building products
Even though IoT solutions are becoming an indispensable part of everyday life, just 0.06% of the things with Internet connection potential are online at the moment. This unexplored landscape represents foundations for further evolution and innovation of IoT solutions and new services.
Smart home is the most popular IoT use case currently. Smart homes popularity is probably driven by the fastest growing age group of new homeowners – the Millennials. Having grown up with technology, they often find it more important than other traditional new home features. Millennials are more attracted by smart homes and smart buildings solutions, having confidence in technology, supporting its further innovation and development, and having knowledge to widely accepted new services.
Amazon, Google, Apple, Samsung are the most dominant companies in the smart home market, offering all kinds of products, from smart thermostats to smart lighting devices. The rise of energy or other utilities production and distribution costs, decreasing cost of technologies and massive production, ongoing government policies, campaigns for energy consumption savings, increasing awareness of the carbon footprint consequences for the environment are great motivation for increasing popularity of smart home devices.
Smart lighting systems, like Hue from Philips, can detect presence of people and adjust lighting as needed. Smart light bulbs are supported with auto-regulation based on sunlight intensity.
Nest from Nest Labs Inc. is a representative example of a smart thermostat. It comes with embedded Wi-Fi, allowing users to schedule, monitor and remotely control home temperature. Smart thermostats can also report about energy consumption or remind users about maintenance issues, filters changes, etc.
Smart locks are perfect support for users to allow or deny access to their premises. With smart security cameras, real time home monitoring becomes available 24 hours a day. Smart motion sensors, supported with many features and setting options, can also make a difference between residents, visitors, pets and unauthorized visitors. They can notify authorities about suspicious activities and activate day or night cameras for recording or even provide monitoring that can help seniors to remain at home comfortably. These safety features are extendable even to pet care.
Smart homes also include use cases such as smart TVs, smart washing machines and dryers in the laundry rooms or different kitchen appliances like smart coffee makers, smart toasters, smart refrigerators that monitor expiration dates, make shopping lists and even create recipes based on currently available ingredients.
One of the most important devices in smart homes is a smart home hub. It represents the central point of the smart home system capable for wireless communications and data processing. It combines all separate applications into a single comprehensive application capable of controlling the smart home. Some available smart home hub solutions are Amazon Echo, Google Home, Insteon Hub Pro, Samsung SmartThings, Wink Hub, etc. Artificial intelligence (AI) technology is implemented in smart homes as well, such as in voice-activated systems like Amazon Echo or Google Home that are illustrated in Figure 4.

They have embedded virtual assistants capable of learning users’ behavior and personalizing the smart home patterns and context.
Generally, IoT solutions apply to smart buildings as a next logical step. Majority of technologies applicable to smart homes are implemented in smart buildings such as lighting systems, security and access systems, identity management or heating and air conditioning systems. Smart buildings generally increase the quality of everyday life by enhancing digital experience, tenants’ satisfaction and staff business efficiency, enabling real-time information, improving life organization and work productivity.
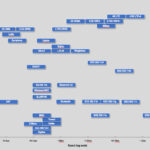
Review of wireless technologies and their applicability for smart home / smart building use cases
The primary task of wireless communication technologies is to provide connectivity for automation. Wireless communication technologies differ in specific capabilities which make them more or less suitable for particular use cases.
One of the first wireless communication protocols developed for home automation support and communication among electronic devices was X10 released in 1975. It provided wireless communication at 120 kHz via digital bursts between programmable outlets or switches. This precursor of modern wireless technologies in the beginning had some drawbacks and disadvantages compared to present-day solutions. It was a simplex one direction communication, because home devices did not have the capability to generate backlink response. Wireless communication in both directions was later enabled via X10 protocol, but it was not a cost-effective solution. Moreover, there was a serious problem of communication reliability because of a signal loss caused by circuits that were wired on different polarities.
In the meantime, thanks to the continuous development of different wireless communications and their convergence with cellular communications driven by the adoption of IoT technologies, home automation continued growing.
Today’s wide availability of wireless technologies (like Bluetooth, ZigBee, RFID or NFC) at a reasonable price is a catalyst for rapid development and implementation of a myriad of smart home IoT use cases.

Wireless communication technologies work on different frequencies, use different modulations, differ in ranges, have different resistance to obstacles and interference, they have different power consumption and different power supply solutions, support different mechanisms for security and communication reliability, etc. All these features influence suitability for particular use cases.
Let’s briefly describe some representative wireless communication technologies like Bluetooth, Zigbee, Wi-Fi, RFID and NFC with their strengths, challenges and applicability for smart homes and smart buildings.
For more wireless protocols, check out my list of IoT wireless protocols.
BLE (Bluetooth)
Bluetooth is a short-range wireless communications technology based on the IEEE 802.15.1 protocol. It works in a crowded license-free 2.4 GHz frequency band and shares this resource with many other technologies.
Bluetooth is the optimal solution for establishing small wireless networks called Piconets, by connecting two Bluetooth devices. One of these nodes is Master that can be connected via Bluetooth link to 7 other Bluetooth devices—Slave nodes in Personal Area Network (PAN). Typical data rates are 1-3 Mbps.
The newest versions of Bluetooth is known as Bluetooth Low Energy (BLE) or Bluetooth smart.
It is important to note that Bluetooth and BLE are not compatible technologies. For example, channel bandwidth in Bluetooth technology is 1MHz and in BLE is 2MHz, number of channels in Bluetooth is 79, while BLE supports 40 channels. They also differ in waveforms, transmission power, network organization etc. Bluetooth Versions 4.1/4.2/5.0 support both BLE and Bluetooth standards, but if the master device is a BLE device, the slave must also be a BLE device.
In the most recent Bluetooth Version 5.0 new wave-forms and coding techniques are implemented to achieve longer ranges of 50m or more, less power consumption, lower latency, better robustness and support for a higher number of subscribers in a single Bluetooth network.
At its inception the Bluetooth technology was used for data streaming or file exchange between mobile phones, PCs, printers, headsets, joysticks, mice, keyboards, stereo audio or in the automotive industry.
These days BLE technology became an indispensable protocol used in mobile phones, PCs and other types of devices applicable in gaming, sports, wellness, industrial, medical, home and automation electronics. It is an important wireless technology for smart homes and smart buildings because of the achieved ranges, throughput (2 Mbps), reliability, security performances, low power transmission and low power consumption. BLE provides wireless connectivity that enables home automation via the control of lights—smart bulbs and outlets, smoke detectors, cameras and other security systems, thermostats, video door bells, smart digital locks, hubs and controllers, different assistant devices, universal remotes, gaming consoles, TVs, etc.
In smart buildings, this wireless technology enables automation of some complex systems, as presented in Figure 2, such as: Heating, Ventilation and Air Conditioning (HVAC), lighting, security and indoor positioning. BLE technology deployed in smart buildings enables optimal space utilization, lowers operating and maintenance costs by condition monitoring via different sensors, contributes to energy savings, enhances the tenants, staff or visitor experiences, etc.

BLE is important for both residential and business buildings. It changes the outlook of the offices by formatting the smart meeting spaces or enabling the sensor-based occupancy mapping, improves workflow efficiency, reduces expenditures, increases revenues and employee satisfaction. In specific smart building types—smart healthcare facilities or smart hospitals, BLE is crucial for patient care and operational efficiency improvements.
In retail industry, coupled with beacon technology, it supports enhanced customer services like in-building or in-store navigation, personalized promotions and specific customer oriented content delivery. Some BLE limitations for smart home and smart building use cases would be: suitability for short range controls only, interference with other wireless technologies (Wi-Fi, Zigbee, etc.) that are using license free 2.4GHz frequency range, optimal for short-burst wireless communication, lower throughput compared to some other wireless technologies, lack of generic IP connectivity etc.
Zigbee
Zigbee is wireless PAN (Personal Area Network) technology developed from IEEE 802.15.4 wireless standard and supported by the Zigbee Alliance. IEEE 802.15.4 standard defines the physical and data link layers with all details about the robust radio communication and medium access control. Zigbee Alliance provides content standardization of the transmitted messages from network layer to application layer. It is a non-profit association, responsible for open global Zigbee standards development. Companies like Google, Amazon, Qualcomm, Samsung, Silicon Labs, Philips, Huawei, Toshiba etc. are members of Zigbee Alliance.
The Zigbee wireless communications technology operates in unlicensed frequency bands including 2.4 GHz, 900 MHz and 868 MHz, within 100m range. It enables up to 250 Kbps throughput in the 2.4 GHz frequency band and 40 Kbps/20 Kbps in the 900/868 MHz frequency bands. In the 2.4 GHz frequency band the Zigbee technology is organized in 16 channels, shifted in 5MHz steps. This technology supports theoretically up to 65000 nodes organized in a single wireless network. There are three types of nodes – logical devices in a Zigbee network:
- Zigbee Coordinator – is a device responsible for establishing, executing, administering and managing the overall Zigbee network, its security, subscribers list, etc. There is only one coordinator in Zigbee network.
- Zigbee Router – is an intermediate node responsible for routing packets between end devices or between end devices and the coordinator. In one Zigbee network there could be several routers.
- Zigbee End Device – represents a sensor or a node that monitors and collects required data. Unlike routers or coordinators, these nodes are usually battery operated. Hence, they could be put to sleep for a certain period to minimize battery draining and conserve energy when there is no activity to be monitored. End devices can neither route traffic nor permit other nodes to join the network.
Zigbee technology supports three types of network topologies—star, mesh and hybrid mash.
- In a star network, one hub, the coordinator is the central point of all communications, limiting the network coverage with its range and processing power. As the most important node in a Zigbee star topology network, it represents a single point of failure.
- In the mesh network all end nodes are router nodes at the same time, including the coordinator after the network initialization, making this topology robust and without a single point of failure (presented in Figure 3).
- Hybrid mesh topology combines the first two types—in this topology there can be several star networks and their routers can communicate as described in a mesh network.
We must consider the choice of topology in the network planning phase, taking into account its purpose, available power supply solutions, range and throughput requirements, schedule for end nodes (sensors) activity, costs and other factors important for specific use cases.
In the endless process of technology evolution, the Zigbee Alliance continues improving Zigbee standard. The latest version of Zigbee standard has enabled interoperability among the wide range of smart devices from different manufacturers and provides access for end-users to innovative products and services that will work together seamlessly.
Today Zigbee 3.0 is one of the most common wireless standards implemented in IoT devices. It significantly affects smart homes and smart buildings development because of the low power consumption, long battery life, built–in support for mesh networking and IP, provided communication security and reliability, cross-band communication across 2.4GHz and sub-GHz frequency bands, etc. Zigbee became one of the most crucial technologies and a global standard for home automation. It helps creation of smart home, by enabling appliances control, improvements in everyday comfort, security and energy management.
As the Zigbee 3.0 devices have energy harvesting support and long battery life, we generally describe this technology as the low-power Wi-Fi.
Its applicability in smart homes and smart buildings enabled remote control of different equipment like smart plugs or motion sensors, light switches, thermostats, door locks and systems like security, HVAC and energy or water consumption.
Worldwide compatibility is enabled between the Zigbee 3.0 devices which improves inherited interoperability challenges. At the same time, operating and maintenance costs are decreased, making it a win-win solution for both—end users (staff, tenants or visitors) and providers.
Zigbee is the standard of wireless technology choice for smart home and smart building applications, but some of its disadvantages are recognized as well, such as short range communication, data throughput that is optimized for bursts of sensor transmissions but not for streaming, lack of advanced error correction mechanisms, sometimes more complex troubleshooting, star topology single point of failure, etc.
Wi-Fi
The Wi-Fi represents wireless technology that includes the IEEE 802.11 family of standards (IEEE 802.11a, IEEE 802.11b, IEEE 802.11g, IEEE 802.11n, IEEE 802.11ac, etc.). Within 50m range, it operates in 2.4 GHz and 5GHz frequency bands.
This technology was developed for wireless networking of computer devices and is commonly called WLAN (Wireless Local Area Network), where the communication is realized between wireless routers typically connected to the Internet and other wireless nodes within its range.
In compliance with performances of specific IEEE 802.11 standards, different data rates are enabled and their theoretical throughput is 11 Mbps (IEEE 802.11b), 54 Mbps (IEEE 802.11a and IEEE 802.11g), 100 Mbps (IEEE 802.11n) or 300 Mbps (IEEE 802.11ac).
In the overcrowded 2.4 GHz frequency band, there are 14 channels dedicated for the Wi-Fi technology. In 5 GHz frequency band, RF channel distribution for Wi-Fi is correlated with national legislation and RF bands allocation plans.
A new Wi-Fi HaLow (IEEE 802.11ah) standard is a technological successor of the current IEEE 802.11ac wireless protocol. It works at 900 MHz frequency band in the USA and significantly improves wireless coverage and energy efficiency as one of the most important features for smart homes, smart buildings and other IoT use cases.
Among other available choices, this technology is used in smart homes and smart buildings for use cases with high throughput audio/video streaming requests, centralized management applications, video monitoring and security systems, etc. Networking of multiple devices such as cameras, lights and switches, monitors, sensors and many others is enabled with this technology.
One of the major Wi-Fi benefits is its prevalence in almost all digital devices today and capability to provide high-capacity wireless links. From a security perspective, activation and implementation of supported encryption mechanisms provide acceptable protection, like Wi-Fi Protected Access (WPA) or WPA2. Wi-Fi technology enables generic IP compatibility, easy installation and operation procedures, possibility to add or remove the devices to or from a network with no particular management efforts and impacts to network functionality, efficient troubleshooting, etc.
This technology can be implemented as a back-end network for offloading aggregated data from a central IoT hub to the cloud, which is a very important feature applicable to smart homes and smart buildings.
Some Wi-Fi drawbacks for smart home and smart building use cases are power consumption, higher infrastructure price, susceptibility to obstacles that limits the range, susceptibility to RF jamming—important for smart home or smart building security systems, available throughput is shared between connected devices, susceptibility to interference from the many devices that operate at the same frequency—including Wi-Fi and other wireless technologies devices like cordless phones, microwaves, etc.
Radio-Frequency Identification (RFID)
Radio-Frequency Identification (RFID) is a technology commonly used for identification, status administration and management of different objects. It is important for people identification, as it is commonly deployed in latest biometric passports.
It operates in several frequency bands like Low frequency band from 125 kHz to 134 kHz, High frequency band with 13.56MHz working frequency, Ultra-high frequency band with 433 MHz working frequency and 860 – 960 MHz sub-band.
In Ultra-high frequency bands there are two types of RFID systems—Active and Passive.
- Active RFID system operates on 433 MHz radio frequency and on 2.4GHz from Extremely High- Frequency Range. It supports range from 30 to 100+ meters.
- Passive RFID system operates on 860 – 960 MHz frequency and supports up to 25m range.
Commonly, a RFID system has three major components: RFID tag, RFID reader and RFID application software.
- RFID tags can be active (with microchip, antenna, sensors and power supply) or passive (without power supply).
- RFID reader is another hardware component that identifies a RFID tag and transmits its status to the RFID software application.
- RFID software applications (often mobile applications) monitor and administer RFID tags. They usually exchange information with RFID readers via different beacon technologies or Bluetooth.
RFID technology is very important for different IoT applications including smart homes and smart building. According to the applied frequency ranges, some advantages and limitations of RFID systems are given in Table 1.
| RFID system type | Advantages | Limitations | Applicability |
| Low frequency band |
|
|
Animal tracking, access control, applications with high volumes of liquids and metals. |
| High frequency band |
|
|
DVD kiosks, library books, personal ID cards, gaming chips, etc. |
| Active RFID systems |
|
|
Vehicle tracking, auto manufacturing, mining, construction, asset tracking. |
| Passive RFID systems |
|
|
Supply chain tracking, manufacturing, pharmaceuticals, electronic tolling, inventory tracking, race timing, asset tracking, etc. |
RFID tags are implemented as an interface between the IoT ecosystem and the subscribers. This technology potential is significant because of its low cost and low power features.
Smart clothes are a representative example of RFID technology deployment in a smart home. Garments with embedded RFID tags could share information with smart home appliances, to help us improve life quality. Smart bins could help to sort clothing items into logical groups, while balancing the load size. Smart washing machines in smart homes or buildings could read the embedded RFID tags on smart clothes and set the optimal wash cycle in compliance with provided instructions. Smart cleaning/laundry services provided in smart buildings can establish real-time communication with the building tenants, keeping them informed about the status of requested service.
RFID is also important for indoor location applications development and Angle of Arrival (AOA) technology. AOA technology implies the optimization of the mobile tag signals arrival angle from at least two adjacent sources, establishing a real-time location system with centimeters accuracy. In the context of localization systems and indoor applicability, this is a significant improvement.
RFID technology enables new consumer applications and services for smart homes and buildings like smart shelves, smart mirrors, self check-in or check-out, restricted area access control, etc.
Some important RFID technology advantages for smart home and building applications are low cost, low power consumption, great implementation potential, perspective for development of different user friendly software (mobile) applications, etc. RFID technology limitations are susceptibility to interference caused by different objects or eavesdropping and DDoS attacks, lack of standardization support, signal collision, etc.
Near field communications (NFC)
NFC is a short range two-way wireless communication technology that enables simple and secure communication between electronic devices embedded with NFC microchip. NFC technology operates in 13.56 megahertz and supports 106, 212, or 424 Kbps throughput. There are three available modes of NFC communication:
- Read/write (e.g. for reading tags in NFC posters)
- Card emulation (e.g. for making payments)
- Peer-to-peer (e.g. for file transfers)
There is no need for pairing code between devices, because once in range they instantly start communication and prompt the user. NFC technology is power efficient – much more than other wireless technologies. The communication range of NFC is approximately 10 centimeters and it could be doubled with specific antennas. The short range makes this technology secure. Only allowing near field communications makes this communication technology optimal for secure transactions, such as contactless payments. Some examples of NFC applicability include:
- Ticket confirmation for sports events, concerts, at theaters, cinemas;
- Welfare performances improvement – syncing workout data from a fitness machines with personal user device;
- Personalized content sharing – viewing special offers on your phone in museums, shopping malls and stores;
- Loaders of translated content in different services, like menus in the restaurants;
- Check-in and check-out in hotels, airports, etc.;
- Security systems – unlocking an NFC-enabled door locks, etc.
NFC technology provides further support for smart home and smart building evolution. In the bedroom an NFC tag can be used for monitoring TV, wireless system, alarm, lighting or other devices via the smartphone. In the kitchen NFC tags could be placed on refrigerator and oven making them smart as presented in Figure 3., or they could be used to modify the ambient according to your needs (turning on and off some lights, music, etc.)

NFC tags can transform a smartphone or other personal digital device embedded with NFC chipset, into a universal remote capable of performing any action. Compared to RFID technology, every NFC device has embedded NFC reader and NFC tag capabilities. The potential for NFC technology applicability in smart homes and buildings is endless.
NFC advantages for smart homes and buildings applicability are simplicity, security, capability to connect unconnected devices via NFC tags or bridge other incompatible wireless technologies, low power consumption, widespread technology in almost all electronic devices, etc.
The main limitations that have to be considered for NFC applicability in smart home and smart building use cases are: very short distance, lower throughput compared to other wireless technologies, it is not completely risk-free technology – due to the fact that mobile based hacking tools are evolving and became common today.
Built-in cybersecurity features of wireless technologies (Bluetooth, Zigbee, Wi-Fi, RFID and NFC)
Traditionally, wireless networks are self-contained, homogenous and do not provide interoperability between different wireless technologies. There is no single wireless technology optimal for all use cases, capable of supporting all coverage, throughput, mobility, etc. requirements. As these technologies are wireless and susceptible to security issues, security protection is one of top priorities and the most challenging features in wireless networking. Rapid development and increasing importance of all wireless technologies became crucial for the fourth industrial revolution (IoT). Communications infrastructure is more complex than ever before. This trend will continue.
Hence, the general conclusion is that the principal task of wireless communication technologies should be to provide secure connectivity. In this chapter I’ll present some representative security features and challenges of above-mentioned wireless technologies.
BLE (Bluetooth) Cybersecurity
Several security modes are recognized in Bluetooth technology. Each version of Bluetooth standard supports some of them. These modes differ based on the point of security initiation in Bluetooth devices. Bluetooth devices must operate in one of four available modes:
- Bluetooth security mode 1 – it is an insecure mode. It is easy to establish wireless connectivity in this mode, but the security is an issue. Bluetooth security mode 1 applicability is in short range devices and only supported up to Bluetooth v2.0 + EDR (Enhanced Data Rate) standard version.
- Bluetooth security mode 2 – a centralized security manager is responsible for access to specific services and devices in this mode, by implementation of the authorization procedure. All Bluetooth devices can support this security mode. However, v2.1 + EDR devices support it only for backward compatibility.
- Bluetooth security mode 3 – in this link level-enforced security mode, the Bluetooth device initiates security procedures before establishment of physical link. It uses authentication and encryption for all connections to and from the device. Bluetooth Security Mode 3 is only supported in Bluetooth devices with v2.0 + EDR or earlier versions.
- Bluetooth security mode 4 – in this mode security procedures are initiated after link setup. Secure Simple Pairing uses Elliptic Curve Diffie Hellman (ECDH) techniques for key exchange and link key generation. This mode was introduced at Bluetooth v2.1 + EDR.
Following five basic security services are implemented in Bluetooth technology:
- Authentication – verifies the identity of devices that are exchanging data, based on their Bluetooth address.
- Confidentiality – ensures that only authorized devices can access and view transmitted data. It is important for preventing compromise of information, for example caused by eavesdropping.
- Authorization – ensures that Bluetooth devices are authorized to use the service.
- Message Integrity – verifies that a message sent is a message received, without any changes in between its source and destination.
- Pairing/Bonding – creates and stores shared secret keys important for a trusted device pair establishment.
Supported security mechanisms developed together with standard versions. In compliance with the Bluetooth Specification Version 5.0, two security modes are implemented in BLE: Security mode 1 and Security mode 2. Within each of them, there are different security layers. BLE security mode 1 has 4 layers:
- No security (without authentication and without encryption).
- Unauthenticated pairing with encryption (AES-CMAC encryption or AES-128 -is implemented in this layer, during communications when the devices are unpaired).
- Authenticated pairing with encryption.
- Authenticated BLE secure connections pairing with encryption (each time after the pairing is initiated Elliptic Curve Diffie-Helman key agreement protocol is used for key exchange BLE secure connections).
BLE security mode 2 is supported with 2 layers:
- Unauthenticated pairing with data signing.
- Authenticated pairing with data signing.
Security manager protocol, built in the session layer of the OSI reference model, is responsible for pairing, signing between nodes, encryption, key administration, key management, security services management and all other security features in a BLE network. Bluetooth has some security vulnerabilities, as does any other wireless technologies. Its implementation has to be planned taking into account possible security threats. Some representative security challenges of BLE (Bluetooth) technology are:
- Passive eavesdropping and Man in the Middle (MITM) attacks or identity tracking apply to Bluetooth technology. The interception of radio waves between a smartphone and smart lock can be realized by a different kind of sniffers. Their price range today is 50-100 USD.
- Bluejacking involves the sending of a vCard message via Bluetooth to other Bluetooth users within the short ranges – typically 10 meters. The risk is that the recipient will not realize what the message is and it is possible to open messages automatically, assuming that they are sent from someone known from the contact list.
- Bluebugging is the Bluetooth security issue that allows unauthorized remote access to a phone and usage of its features. It may include placing calls and sending text messages. In the meantime, the owner does not realize that his phone has been taken over. Depending on the attacker’s creativity, denial of service (DoS) attacks and resource misappropriation are consequences of this security issue, too.
- Car Whispering is a hacking technique that implies the usage of specific software to send and receive audio and other files to and from a Bluetooth enabled car stereo system, to invade privacy or listen conversation. It could be applied in the same manner to a Bluetooth enabled systems in smart homes or smart buildings.
- Bluesnipping is a hacking technique capable to extend the range of unauthorized Bluetooth communication system monitoring and provide malicious coverage within a mile distance. It is realized with a specific hardware – a Bluesnipping gun that is made with a few hardware pieces like folding stock, Yagi antenna and Linux terminal.
These vulnerabilities can cause unauthorized access to sensitive information, unauthorized use of Bluetooth devices and other systems or networks to which the Bluetooth devices are connected. In order to protect a network from security vulnerabilities, it is always useful to be careful with third-party applications and install applications only from trusted sources. Recommendation is to deploy a home network firewall that will protect and encrypt all incoming and outgoing data.
Zigbee Cybersecurity
The Zigbee Alliance and its members are continuously improving security performances of Zigbee technology, to achieve optimal balance between deployment, exploitation and security requirements in wireless machine to machine communication.
Zigbee is considered to be a relatively secure wireless communication protocol, with security architecture built in accordance with the IEEE 802.15.4 standard. To meet the security needs, Zigbee provides a standardized set of security specifications based on a 128-bit AES algorithm and compatible to wireless 802.15.4 standard.
Security mechanisms include authentication, authorized access to network devices, integrity protection and encryption with key establishment and transportation. Device authentication is the procedure of confirming a new device that joins the network as authentic. The new device must be able to receive a network key and set proper attributes within a given timeframe to be considered authenticated. Device authentication is performed by the Trust Center. Integrity protection is realized on the frame level using message integrity checks (MIC) to protect the transmitted frames and ensure they are not accessed and manipulated. A 128-bits symmetric-key cryptography is implemented in Zigbee’s security architecture. Zigbee technology supports 3 different types of keys for different purposes:
- Master key must be obtained by pre-installation, secure key transport or user-entered data such as PIN or password. It is used for link keys derivation and establishment.
- Network key is used for network establishment and broadcast network communication. This key provides network level security.
- Link key is used for encryption point-to-point communication at the application level. It is different for each pair of devices in the network that are working in point-to-point mode. Link keys are used to minimize the security risks of Master key distribution. This key provides APL level security and the messages between devices are protected with both – the Network key and the Link key.
There are two types of security models in Zigbee networks. They mainly differ according to the implemented mechanisms, i.e. how new devices are admitted into the network and how they protect the messages in the network – Centralized security network and Distributed security network.
In the Centralized security model only Zigbee Coordinator with Trust Center credentials can establish centralized networks. Nodes join the network, receive the network key and establish a unique link key with the Trust Center.
In the Distributed security model, there is neither Zigbee Coordinator with Trust Center credentials nor Master keys. All the nodes in the network are pre-configured with the Link key, before entering the network and using the same network key for message encryption.
Zigbee technology supports different key management and transportation mechanisms, such as pre-installation (realized by manufacturer), key establishment—a method of generating Link keys based on the Master key, and key transport—when the network device makes a request to the Trust Centre for a key.
Security attacks and unauthorized usage are possible, as Zigbee technology applies to remote control and monitoring of sensitive resources, infrastructure or home security. Some important security issues in Zigbee networks would be:
- Replay and injection attacks. In the first phase, specific tools for Zigbee network discovery transmit beacon request frames and analyze responded information about available nodes in the network. This entire process finds Zigbee devices working on dedicated working channels, sends and receives beacon request and response frames over that single channel. Next phase is capturing the packets, analyzing them, then replaying the same packets and making it look as if they came from the originating node to cause a change in the device’s behavior, determined by the replayed packets. The network will treat the malicious traffic as regular traffic.
- Wormhole attacks exploit the mechanisms to discover routes of on-demand routing protocols and apply to Zigbee networks. A malicious user that receives packets at one point in the network then replays these packets in other areas to interfere with the overall network functionality. The attacker can control the data that flows through the malicious tunnel and launch other attacks, especially if network nodes are far enough from each other.
- Misplacement of some low-cost Zigbee devices with limited protection capabilities – for example, without tamper-resistance (such as temperature sensors and light switches), makes them vulnerable for unauthorized access to privileged information like keys, network identification, working channels etc.
- Zigbee uses the same security level in all network devices for the purpose of achieving and maintaining the device interoperability. This could lead to some security risks.
- Eavesdropping applies to Zigbee networks, especially to ones supported by OTA firmware upgrade capability. This kind of attack is very hard to discover.
- DDoS attacks at the MAC layer are a realistic scenario. If an attacker floods a radio channel with frames, the network will be forced to deny any communication between devices, because Zigbee uses CSMA/CA mechanism and devices always check if a channel is busy before transmission if it is running in non-beacon mode.
- Without integrity protection provided by MIC, a rogue device could modify a transmitted frame and the modification may not be detected by the recipient.
- A denial-of-service (DoS) attack causes a node to reject all received messages. In a Zigbee network, DoS attack can be done by altering routing tables to redirect all or some of the network traffic to a malicious device (sinkhole attack). It is achieved by purposely sending messages to build artificial routing paths or to implement loops to the routing process of legitimate nodes. As a consequence, transmission of packets among devices is hampered.
- DoS attacks could be realized too, by using jamming techniques to trick the user for initiation of a factory reset and preventing the devices from communicating. It could be also realized by sending a “reset to factory default” command to the device and waiting on the device to look for another Zigbee network to connect.
- Upon leaving the network, a node can still access the communication, since it still possesses the master and link keys. If we analyze an example of a smart home or smart building where Zigbee devices are used for opening doors or improving energy efficiency, it is not impossible that one or many of the devices are lost or stolen. For that reason, if the keys stored on the devices are not properly revoked, someone might take advantage of the situation and exploit this weakness. Therefore, this type of attacks together with network physical security should not be underestimated and must be taken seriously.
In order to meet the increased security requirements for smart home and smart building use cases, the Zigbee Alliance is permanently engaged in security improvements (new algorithms and functions research and development, security protocols and hardware and software support requirements, networks and system organization and settings, regulatory topics and standards establishment).
Wi-Fi Security
The Wi-Fi Alliance enables the implementation of different security solutions across Wi-Fi networks through the Wi-Fi Protected Access (WPA) family of technologies. Simultaneously with Wi-Fi technology, deployable for personal and enterprise networks, security capabilities evolve too.
Today there are several available levels of security applicable to Wi-Fi networks implemented in WPA protocols, like WPA3 – Personal, WPA3 – Enterprise, WPA2, Open Wi-Fi and Wi-Fi enhanced open.
WPA3 security protocol
WPA3 is the latest generation of Wi-Fi security protocol. It is a successor of successful and widespread WPA2 protocol.
WPA3 adds new security features to deliver more robust authentication, enable increased cryptographic strength for highly sensitive information exchange and support resiliency of mission critical networks.
Once implemented, WPA3 protocol represents best security practices in Wi-Fi networks, while disabling obsolete security protocols and requiring usage of Protected Management Frames (PMF) at the same time. It includes additional features specifically to Personal or Enterprise networks and maintains interoperability with WPA2 protocol.
WPA3 is currently an optional certification for Wi-Fi certified devices that will become mandatory in compliance with the market needs and growth.
WPA3-Personal protocol enabled better protections to individual users by providing more robust password-based authentication. This capability is enabled through Simultaneous Authentication of Equals (SAE), which replaces Pre-Shared Key (PSK) in WPA2-Personal protocol. Some of its advantages are natural password selection (allows easy to remember passwords), protection of data traffic even if a password is compromised after the data was transmitted and easy to use.
WPA3-Enterprise protocol is developed specifically for enterprises, governments and financial institutions, offering an optional mode that uses 192-bit minimum-strength security protocols and cryptographic tools for better protection of sensitive data. It is supported with authenticated encryption (256-bit Galois/Counter Mode Protocol – GCMP-256), key derivation and confirmation (384-bit Hashed Message Authentication Mode with Secure Hash Algorithm – HMAC-SHA384), key establishment and authentication (Elliptic Curve Diffie-Hellman – ECDH exchange and Elliptic Curve Digital Signature Algorithm – ECDSA, using a 384-bit elliptic curve) and robust management frame protection (256-bit Broadcast/Multicast Integrity Protocol with Galois Message Authentication Code – BIP-GMAC-256).
WPA2 security protocol
WPA2 protocol provides security and privacy to Wi-Fi networks since 2006. It is a well-known successor of an obsolete WPA security protocol. The major improvement in comparison with WPA is deployment of stronger AES encryption algorithms in WPA2 protocol.
During 2018, to meet security requirements in evolving networking environments, Wi-Fi Alliance augmented existing WPA2 protocol through configuration, authentication and encryption enhancement. By these enhancements, susceptibility to network misconfiguration is reduced and security of managed networks with centralized authentication services is supported.
Open Wi-Fi networks
In some use cases, open Wi-Fi networks are the only available option. It is important to be aware of the risks that open networks present. To address these risks, Wi-Fi Alliance has developed a Wi-Fi Enhanced Open as a solution for users of open Wi-Fi networks.
Compared to traditional open networks with no protection, Wi-Fi Enhanced Open certification provides unauthenticated data encryption to subscribers. It is based on Opportunistic Wireless Encryption (OWE) method defined in the Internet Engineering Task Force (IETF) RFC8110 specification and the Wi‑Fi Alliance Opportunistic Wireless Encryption Specification. Wi-Fi Enhanced Open enables data encryption that maintains the open networks ease of use and benefits network providers because of simple network maintenance and management.
The intensive evolution of security features in Wi-Fi technology makes it very deployable in the IoT domain and specifically to smart home and smart building use cases. Like other wireless technologies, it has some security challenges too. If we take into account the number of devices embedded with Wi-Fi chips, this becomes even more important. Some representative Wi-Fi security challenges are:
- Jamming susceptibility – a Wi-Fi signal can be easily jammed today. In smart homes or smart building, this attracts additional attention. If a home security system is based on Wi-Fi technology, intruders could effectively block the Wi-Fi signal and disable the alarm system.
- Because of the single point of failure (wireless router or Access Point), DoS attacks are potential risks for smart homes or smart building Wi-Fi networks. If the Access Point is out of service, there is no service availability and complete wireless network is malfunctioning.
- Eavesdropping is performed by simply getting within range of a target Wi-Fi network, then listening and capturing data. This information can be used for a number of unauthorized activities including attempting to break existing security settings and analyzing non-secured traffic. It is almost impossible to reliably prevent this category of attacks because of the nature of a wireless network. It is always important to set the complex parameters in security mechanisms.
- Evil Twins or Rogue Wi-Fi Hotspots are one of the most common ways for obtaining sensitive information from Wi-Fi networks. It represents a fake Wi-Fi access point that imitates the legitimate one. In this scenario, an SSID is state similar to original Access Point and any information disclosed while connected to Rogue Wi-Fi Hotspot could be misused.
- Packet Sniffers – by using a packet sniffer, it is possible to identify, intercept, and monitor web traffic over unsecured Wi-Fi networks and capture personal information such as login credentials to bank accounts and corporate email accounts.
- File-Sharing – if enabled on devices, it can be used for unauthorized access to a device connected to the Access Point or Wi-Fi hotspot and malware drop.
- Malware and Ransomware susceptibility of public Wi-Fi hotspots that could be a part of smart building. Without the protection of AV software and web filters, malware can be silently downloaded.
- A generic IP nature of Wi-Fi networks makes them a perfect surrounding for the testing of the new hackers’ tools and for improvements of the existing ones.
To maintain worldwide interoperability and secure communications between devices from different manufacturers, Wi-Fi alliance permanently improves the security solutions implemented in Wi-Fi technology, provides product certifications, forward and backward compatibility. This approach is very important for Wi-Fi support to different IoT use cases and particularly for smart homes and smart buildings evolution.
RFID Security
RFID technology is becoming increasingly popular for smart homes, smart buildings and other IoT use cases. RFID is considered to be the successor of the barcode technology.
If any of the security mechanisms in RFID is not implemented properly or not operational, the security is broken. Particularly in smart homes and smart building use cases, it may result in unauthorized access to personal data, or even personal tracking.
Like other wireless technologies, RFID is exposed to security threats and the most typical RFID security challenges are:
- Interference susceptibility is caused by environmental factors such as radio noise and collision caused by metal and liquids. The interference affects the RF propagation and eventually leads to error in localization services, propagation, ranges, service availability etc.
- Tag isolation is technically the simplest attack, and the most represented. It includes the jamming of tag communications and blocking data that has to be transferred to the reader.
- Tag cloning includes eavesdropping, the extraction of the unique identifier (UID) and/or the RFID content and their insertion into another tag. Tag cloning is commonly used for unauthorized access to restricted areas or even for changing – decreasing the price of certain goods in supermarkets.
- Relay/Amplification attacks consist in unauthorized amplification of the RFID signal by using a relay and extending the range of the RFID tag beyond the borders of its coverage zone.
- Denial of Service (DoS) attacks include the scenario when a tag is flooded with a large amount of information from a malicious source and cannot process the operational signals sent by real tags. Other techniques are based on jamming – emitting radio noise at the RFID system operating frequency.
- Remote tag destruction is realized by RFID zappers able to send energy remotely. This electro-magnetic field can be very high and capable of burning certain components of the tag. Remote tag destruction is possible if the kill password in some tags is misused – first by passive eavesdropping in order to open the kill password and then applying it intentionally to disable the tags.
- Man-in-the-Middle (MitM) attacks, SQL injection, virus/malware and commands injections are possible by placing an active malicious device between a tag and the reader to intercept or alter the communications between both elements and endanger the readers functioning.
- RFID skimming includes the deployment of unauthorized portable terminals, to make fraudulent charges on payment cards.
To provide a secure wireless network, described security challenges have to be taken into account when creating smart home or smart building systems based on RFID wireless technology.
NFC Security
NFC wireless technology enables all objects to connect to the Internet. Its applicability in the IoT domain, to smart home and smart building use cases is crucial, especially if taken into account the fact that all modern personal devices (cellphones, tablets and notebooks) are embedded with NFC chips and their mutual compatibility is achieved.
One of the security mechanisms implemented in NFC is Digital Signature (defined in the NFC Forum Signature RTD 2.0) with asymmetric key exchange. The Digital Signature is a part of the NFC Data Exchange Format (NDEF) message, which includes also a Certificate Chain and a Root Certificate. Each NFC device has a private and a public key. Developed by HID – NFC tag manufacturer, another security mechanism is a Trusted Tag. It fully complies with NFC Forum Tag Type 4 and works with any NFC Forum compatible devices. The Trusted tag is protected from cloning and embedded with cryptographic code generated by every “tap” or click on NFC button. This cryptographic code protects the content of the transmitted information.
NFC technology operates in limited range and includes additional protection like PIN or biometric locks that enable secure data exchange.
Similar to other wireless technologies, NFC is susceptible to some security challenges. Some illustrative examples are:
- General theft of property or losing a device is hard to avoid. The best defense from this threat is to ensure phones, tablets and other personal devices from unauthorized logging and usage.
- Eavesdropping and interception attacks apply to NFC technology.
- Man in the middle attack is possible if there is a malicious device positioned between two NFC devices or in their short range that receives and alters the exchanged information. They can be prevented by remaining aware of unusual devices that are attached or positioned nearby to transactions premises. It is important to ensure that NFC transactions are realized only in official and authorized places.
5G for smart home / smart buildings
Deployment of 5G cellular communication technology establishes a new ecosystem with great potential. These potentials are based on the creation of the most advanced and the most critical communications infrastructure ever, capable of supporting new service possibilities, including efficient information exchange in an IoT context. A new ecosystem outlines are shaped by the availability of 5G technology features such as:
- High speed (1-20 Gbps) data throughput capable of effectively processing augmented and virtual reality (AR/VR) systems, 3D video streaming with 4K /8K resolutions screens, online gaming and other services, etc.
- Ultra-low latency (<1ms) that is of crucial importance for real time services such as telemedicine and healthcare, AR/VR, intelligent transportation, smart homes and industry automation.
- Millimeter-Wave radio communications with new waveforms and massive MIMO (Multiple In Multiple Out) applicability with beam-forming and beam management, due to frequency range – wavelength, size of antenna and spacing characteristics.
- Massive connectivity and dense coverage for vehicles, mobile subscribers, enterprises, IoT etc.
- Very low energy consumption with extremely long battery life (up to 10 years), necessary for IoT M2M (Machine to Machine) communications.
To enable these capabilities, a completely new air interface capable of supporting heterogeneous access networks in different frequency bands and variable bandwidths is provided for 5G networks. Supported by small cells network structure, it ensures ultra-low latency, great indoor and outdoor coverage, localization and service availability. Cloud Radio Access Network (CRAN) model implemented in 5G technology enables split access architecture and deployment of network virtualization. In this new radio access model, a “central” edge cloud location is responsible for some access network functionality, while other functions are realized in the remote locations, enabling the separation of the front and back-haul in the transport network.
Implementation of adaptable software-based architecture technologies especially applicable to the first three layers of OSI reference model – Software Defined Radio (SDR), Software Defined Access (SDA) and Software Defined Networks (SDN) is enabled in 5G networks together with packet core network upgrades. The implementation of these technologies enables Network slicing as a unique 5G attribute. Network slicing manages and processes the creation of multiple virtual networks within shared physical infrastructure and is expected to be a crucial feature that will empower the deployment of different 5G use cases.
Expectations are that 5G will expand boundaries in all domains of modern life such as travelling, driving, production efficiency improvements, smart systems deployment such as smart cities with smart homes, buildings, hospitals, factories, public safety and services management etc. – all areas of human activity.
AI, IoT and 5G technology are intertwined. 5G technology is responsible to provide a network surrounding capable of supporting widespread use of AI and IoT applications and services. AI significantly improves the network management and services availability. Through integration and advancement of these technologies 5G telecom carriers are in position to improve network planning, capacity expansion forecast, coverage auto-optimization, network slicing, CRAN and dynamic cloud network resource scheduling.
AI is recognized as a game changer that will lead the transformation from the current carriers’ management model based on human capabilities to the self-driven automatic network operation and maintenance management mode. At the same time, availability of IoT and AI applications and services is directly correlated with construction of new 5G infrastructure and networks deployment.
When considering smart buildings and smart homes use cases, automation saves time and costs. Automation processing is moved to a higher level with 5G technology.
By supporting massive connectivity, 5G enables the deployment of smart home devices that work automatically, with no additional settings. For instance, by connecting the specific utilities meters to a central network, it is possible for suppliers of energy or other utilities to monitor, detect and respond if any unusual changes in consumption occur in smart landscapes like buildings, homes and cities.
Improvement in security systems performances is expected due to lower latency with high throughput and network reliability that is provided by 5G technology.
Taking into account predictions that over 80% of traffic will be originated by indoor subscribers, indoor coverage becomes extremely important. The small cells structure of 5G networks improves the indoor coverage, compared to other cellular communication technologies and, at the same time influences the evolution of different HD enterprise services, home VR, holographic communication, telemedicine and other new services applicable to smart homes and buildings.
5G security
5G networks are designed not only to enable information exchange between people, but to also connect machines. The security and privacy are a major concern that spans far beyond 5G as the technology with the most complex infrastructure. It is important to be aware that 5G networks will support millions of low-cost sensors that affect the security, too. Considerations in 5G security and privacy developed new trust models, service delivery models, evolved threat environments, and privacy concerns.
To support all new relations between distinct entities in the 5G ecosystem, new trust models have to be established.
The increase of security requirements in areas such as authentication between distinct elements of a complex set, accountability and non-repudiation is expected.
New categories of devices will shape the trust models and extend the wide range of different security requirements applicable to many use cases such as industry automation control devices, smart home devices with associated services, next-generation of personal devices like tablets and smartphones, etc.
New identity management solutions play an important role in defining new trust models, too.
Cloud technology, AI and network virtualization applicability in 5G networks influence the shaping of the new service delivery models. Decoupling software and hardware, separation of the front and back haul in the transport network, third-party applications deployment in the clouds together with some native telecommunications services impact the demands on virtualization with strong isolation properties and force the new security system organization and deployment.
Simultaneously with new performances, new threats and challenges are rising. So are the privacy concerns.
Generally, the level of 5G security is not defined by the number of specified security mechanisms. A multi-stakeholder approach that involves operators, vendors, regulators, policy makers and representatives of 5G subscribers (from different ecosystem segments) is fundamental to the security baseline of trustworthy, cost-efficient and manageable 5G networks. In such a complex landscape standardization is of crucial importance for everyone – enterprises, public safety, industrial automation, smart homes and buildings, etc. Standards defined by entities such as the ISO (International Organization for Standardization), the IEC (International Electro-technical Commission) and the CSA (Cloud Security Alliance) will also impact the technology evolution, applicability, and customers’ services availability. To provide safe and secure wireless connectivity worldwide, new comprehensive security policies have to be created and implemented in 5G technology.
5G security challenges
Similar to other wireless communications, 5G is susceptible to security challenges. 5G even more so.
There are several specific facts that are determining unique 5G susceptibility in security context, such as:
- Network components that are virtualized and potentially deployed on the NFVI (Network Function Virtualization Infrastructure) and cloud components provide dynamic configurations of 5G architecture and need more dynamic and flexible security solutions.
- Complex control of Network slicing – as a completely virtual type of networking deployed through all entities of 5G network.
- Radio access network is vulnerable to all common wireless network security threats such as rogue nodes, modification, altering or injecting user plane traffic, MEC server vulnerability and DoS attacks.
- AI applicability to 5G networks generates the new cybersecurity challenges, such as AI “black boxes”, the inability to test AI for intentional backdoors, or adversarial learning, which is remote reprogramming of the neural network algorithms.
- Since the 5G network is managed by different software – its protection and reduction of API (Application Programming Interface) and other software vulnerabilities within the network became the priority, together with external roaming threats.
- 5G implements edge computing that represents the potential for new security threats. It moves processing from the core and places it at the edges of the network – spatially distributed closer to high-density data sources to 5G.
- The expansion of bandwidth in 5G creates more complex air interface and security challenges like eavesdropping, RF jamming, MitM attacks, complex resources administration and monitoring, etc.
- Vulnerability is increased by attaching billions of smart but often low-cost and hackable devices to an IoT networks and other types of subscriber devices that can suffer from malware, MitM attacks, DDoS (Distributed Denial of Service) and other botnet types of attacks, lack of device tampering protection, snooping and sniffing attacks, etc.
- Protection of subscribers’ personal privacy is a very important component of 5G security that includes access to location information (location based services), data and personal information privacy (personal health information, identity management or employee personal information available for enterprises).
- Quantum technology is expected to break almost all encryption solutions available today. This issue has to be resolved on time, by upgrading encryption models to quantum resilient ones. For example SK Telecom, South Korea’s largest mobile operator has already developed Quantum Key Distribution (QKD) technology for its 5G network.
Without further standardization, regulation and strong proactive measures, 5G networks offer the widest and the most attractive attack surface and remain vulnerable to cyber-attacks.
Conclusion – wireless technologies and IoT perspective
It is impossible to deploy a functional IoT ecosystem without the support of wireless technologies. They provide the communications between the billions of devices, network and applications servers, cloud infrastructure, machines and sensors, subscribers, new applications and services, etc.
The latest cellular communications technology – 5G is recognized as a game changer that will support different heterogeneous wireless technologies, open new perspectives for AI and augmented reality applicability, provide necessary infrastructure that will enable secure and safe deployment for smart homes, smart buildings and smart cities or any other IoT use cases.
5G, as the communications technology with the widest applicability for different IoT use cases, is expected to become the most critical of critical infrastructures ever.
Enabled by 5G, the potential of smart homes, smart buildings, and smart cities will explode. With the wide applicability and ubiquity, the arrival of 5G will further expand the demand for smart home devices, impact their development, lead to more competitive pricing and make them more available in everyday life.
It is essential to pay close attention to the integration and configuration of wireless devices, in compliance with system needs and to achieve secure communication in different IoT use cases. Regardless of the security protocols applied in the wireless – cellular technologies and security solutions implemented across the different layers of OSI reference model, we must also keep the focus on user attention as one of the most important details that significantly contributes to overall system safety and security, especially for smart homes and smart building use cases.
Marin Ivezic
For over 30 years, Marin Ivezic has been protecting critical infrastructure and financial services against cyber, financial crime and regulatory risks posed by complex and emerging technologies.
He held multiple interim CISO and technology leadership roles in Global 2000 companies.